
Sergey Nivens - Fotolia
Explore the revert-to-snapshot feature in OpenStack Cinder
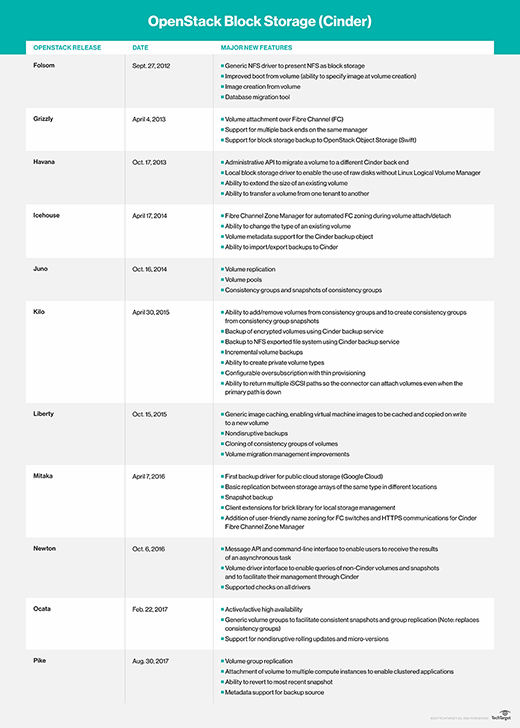
OpenStack Cinder has added a revert-to-snapshot function, enabling enterprises to recover from corrupted data sets. However, if the feature falls into the wrong hands, risks arise.
Storage snapshots provide a quick way to set recovery points on data. Admins typically automate snapshots and perform them frequently to keep recovery point objectives to a minimum, but you can also perform them manually. And now, OpenStack Cinder provides admins with more snapshot options.
There are a variety of uses for storage snapshots. For example, when developers sandbox prototype code, it's common for them to revert to a known initial data set to avoid corrupting the test data. In mainstream operations, admins can also use snapshots to deliver consistent data recovery in the event of ransomware corruption or wholesale data loss.
To set up the revert-to-snapshot feature in OpenStack Cinder, demount the afflicted volume, and then, issue the revert command. The Cinder project team recommends reversion to only your most recent snapshot to prevent out-of-control backtracking, which may occur when multiple storage snapshots are corrupted.
Enterprises need to use this revert-to-snapshot function cautiously. Reversion to a saved snapshot ultimately deletes the current, corrupted data, and any changes that occurred between the saved version and the corrupted version will be lost. An inexperienced user could easily wreak havoc with this; restrict reversion features to senior expert admins, except in sandboxes.
However, there is a proposed feature for OpenStack Cinder that would retain a snapshot of your current, corrupted data. This would enable enterprises to manually recover individual files. While this capability would also make the revert operation more tedious, it could save a lot of data -- again, if you use it carefully.
OpenStack also plans to make the revert operation atomic, which means it prevents any other operations from running while it processes. There is still room for more advanced features, like the ability to recover individual or groups of objects from the storage snapshot or corrupted data set.
Snapshots, in general, are a good way to protect data, but if your disaster recovery and backup approaches rely on them, make sure you keep a geographically distributed copy.








