knowledge management (KM)
What is knowledge management (KM)?
Knowledge management is the process an enterprise uses to gather, organize, share and analyze its knowledge in a way that's easily accessible to employees. This knowledge can include technical resources, frequently asked questions, training documents and other information.
Knowledge management involves data mining and a way to push information to users to make it easily accessible. A knowledge management plan involves a survey of corporate goals and a close examination of the tools -- both traditional and technical -- to address the needs of an organization. The challenge of selecting a knowledge management system is to purchase or build software that fits an organization's overall plan and encourages employees to use the system and share information.
What is knowledge management used for?
The main goals of KM are improving organizational efficiency and saving knowledge in an easily accessible form. Knowledge management aims to put the right information in front of a user at the right time.
This is done by doing the following:
- Capturing and organizing knowledge in a knowledge management system to address specific business tasks and projects.
- Sharing knowledge with others who can benefit from it.
- Improving processes and technology to provide easy access to knowledge.
- Promoting the generation of new knowledge for continual learning.
Knowledge management helps businesses break down silos by putting information in a place easily accessible to all employees. It also gives employees a place to put knowledge they've acquired over time, preventing a business from losing that information when employees leave the company.
Types of knowledge
Knowledge is an understanding of information that an organization or user acquires through education and experience. That information comes from data -- raw facts and figures that have been contextualized.
There are four types of knowledge -- explicit, tacit, implicit and embedded. However, the two most important distinctions are explicit and tacit.
- Explicit knowledge. This type of knowledge is codified -- meaning it's found in books, files, folders, documents, databases, written procedures, checklists and how-to videos -- and is most easily extracted and handled by a knowledge management system. It is, by definition, the easiest form of knowledge to pass along.
- Tacit knowledge. This form of knowledge is intuitive in nature. It's based on experience and practice and often helps in achieving long-term goals. This type of knowledge transfer is difficult, as it lies with a single person. There's no easy way to extract it as with explicit knowledge, leaving the knowledge-holder with the task of writing it down or creating a video. Some examples of tacit knowledge include identifying the right moment to launch into a sales pitch or developing leadership skills. The terms emotional intelligence, intuition and judgment can all be applied to tacit knowledge.
- Implicit knowledge. This refers to the application of explicit knowledge. It includes the explanation of that explicit knowledge and is more difficult to capture.
- Embedded knowledge. This knowledge is found in systemic processes, routines, manuals, structures and organizational cultures. It's embedded formally through management initiatives or informally as organizations use and apply the other knowledge types. While embedded knowledge can be found in explicit sources, it isn't always immediately apparent why doing something in a certain way is important for a business. This is often also referred to as procedural knowledge.
Examples of knowledge management systems
A knowledge management system is a type of content management system that houses and retrieves organizational knowledge. It's commonly known as a knowledge base and helps present information to users in various ways, including the following:
- FAQs.
- Webinars.
- Training programs.
- Case studies.
- Forums or community features.
Examples of knowledge management systems include the following:
- Bloomfire. This knowledge management platform provides artificial intelligence (AI)-powered search and discovery tools as well as an AI-based chat that allows creators to gather material for content with natural language queries. Bloomfire provides KM tools for several industries, including banking and finance, manufacturing and insurance.
- Document360. This tool lets organizations create both public and private knowledge bases. Features include the ability to roll back to previous versions, analytics and reports, advanced security access and third-party integrations with tools such as Microsoft Teams, Zendesk and Intercom.
- DominKnow One. This software focuses on content authoring, particularly in a team context, including streamlined collaborative workflows. It includes tools for easy creation of interactive content, as well as formatting for different device types.
- Guru. This software's AI integration drives its search functionality. It includes an enterprise intranet, which makes knowledge sharing easier, along with its knowledge base, which has a wiki.
- Zendesk Guide. Zendesk Guide integrates with Zendesk Support and provides features including an integrated knowledge capture app, article recommendations, an Answer Bot for internal teams and their customers, and a customer portal.
What is the knowledge management process?
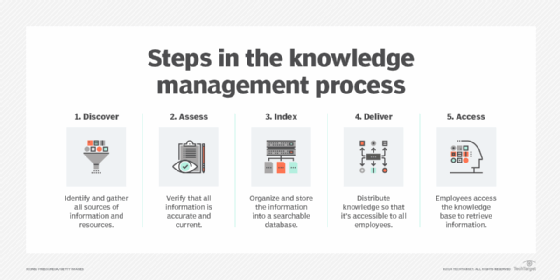
Knowledge management includes the following five key processes:
- Knowledge gathering. This includes entering data, optical character recognition and scanning, pulling information from various sources and searching for other information to include.
- Knowledge assessment. Once data has been discovered and captured, it must be assessed before it can be truly useful. This means it must be examined for incorrect or outdated information, redundancy, and gaps and incompleteness.
- Knowledge storage and organization. This includes cataloging and indexing content in a knowledge management system and placing links within this content to provide further related information for users to digest.
- Knowledge distribution. This provides a way for users to access the information, including FAQs, training videos, white papers and manuals.
- Knowledge use. Once information is distributed to users, they must put it into action.
Benefits and challenges of knowledge management
In addition to reducing business operation costs and increasing employee productivity, knowledge management provides the following benefits:
- Reduces duplication of existing knowledge. Individual and collective knowledge is now recorded and stored in one place that's easily accessible to users.
- Improves employee training. New employees can train more quickly and thoroughly by getting answers to questions that aren't covered in the training material.
- Enhances customer onboarding. As with employee training, new customers can rapidly get answers to questions that might not be covered in onboarding presentations.
- Provides information at users' fingertips. Users no longer need to ask multiple people for the same thing in hopes that they might know the answer to their question.
- Reduces mistakes. As users share information, they work out the kinks of various processes, preventing the same mistake from being made twice.
- Offers standardized processes. A golden record of processes and procedures is stored in a system for all to access, which can improve employee onboarding and training. This also preserves information, preventing processes from getting muddled over time.
- Increases collaboration. With users sharing knowledge in a common space, it's more convenient to work together to improve processes.
There are, however, also some challenges with knowledge management, including the following:
- Resistance to change. Employees are often set in their ways and managers find it difficult to motivate employees to change their habits and share knowledge in a common workspace.
- Obsolete technology. Technology is constantly changing, making it sometimes difficult to keep up with the latest updates and tools.
- Security concerns. As with any information in a business system, user permissions and security levels must be set to ensure the right people are seeing the right information.
- Outdated information. Like technology, information changes rapidly. It's necessary to keep it fresh and relevant.
- Information overload. With so much information, it can be challenging for users to pinpoint the exact information they need.
Knowledge management best practices
Organizations can approach knowledge management in different ways, but implementing the following best practices can put them on the road to success:
- Assess organizational culture. It's important to understand the capabilities and needs of the employees who will be using a knowledge management system before choosing one. If employees only have basic computer skills, for example, an organization should think twice before buying an expensive and complicated system.
- Make effective design a priority. A knowledge management system's navigation and underlying information architecture are critical to its ease of use, ease of maintenance and ultimate success. An organization should consider these aspects of its design by gathering input from as many stakeholders as possible before implementing the system.
- Carefully plan a rollout. Organizations shouldn't bombard employees with new knowledge management processes and systems all at once. They should plan a slow yet deliberate rollout with training at each step in the process to ensure employees are comfortable with the new system and use it.
- Motivate and reward employees. Managers should motivate employees with rewards for using the new knowledge management system. This will encourage knowledge sharing instead of knowledge hoarding.
- Implement knowledge ownership. Attaching employee credit to knowledge documents and media simultaneously motivates employees and provides a breadcrumb trail for other users. If they need clarification or additional information on something they've read or watched, they know who to contact.
- Create a formal knowledge exchange policy. This is important, especially when people leave a company. Instead of losing information along with that employee, they would pass that information along to other employees, ensuring knowledge retention.
Creating and implementing a knowledge management framework
It's necessary to have a plan before implementing a knowledge management framework. Businesses can take the following steps to ensure a smooth rollout:
- Establish program objectives. Leadership should identify what business processes -- such as training and onboarding -- need to be addressed and document short-term and long-term objectives.
- Include employees in implementation process. Employees need to learn the new process and must rethink the way they share knowledge. Businesses should appoint knowledge management champions to assist with this change, motivating others to share knowledge and providing feedback to the implementation team. It might also be useful to consult with selected customers and clients for their input.
- Develop detailed procedures. This includes details about how businesses capture, organize and deliver knowledge. This step also includes creating knowledge management best practices.
- Determine technology needs. Businesses can determine their needs based on their program objectives. They must also understand what technology employees are currently using, what does and doesn't work and why. Organizations should ensure that existing technology isn't already meeting business needs.
- Build a roadmap. Before addressing these technology needs, the business should confirm leadership's support in this endeavor, along with program funding. This roadmap could span months or even years.
- Implement the program. Once processes and technology are in place and the business has addressed its organizational culture, it's time to launch the program.
- Measure success and improve program. Just because a knowledge management program is live doesn't mean the work is done. Organizations must measure the success of their program and make continual improvements for optimal efficiency. They should also create scorecards that address performance, quality, compliance and value. Benefits might not be immediately obvious, but the business will see results over time.
What does a knowledge manager do?
The following are just a few examples of knowledge management job titles and responsibilities:
- Engagement manager. This role helps build strong and long-lasting customer relationships. Providing customers with knowledge resources that answer their questions, assisting them in communicating, and bolstering their confidence in the organization are central to the job.
- Knowledge management technology specialist. This role knows the organization's KM platform inside and out and assists individuals and teams in developing knowledge management strategies for optimization throughout the enterprise.
- Content manager. This role can include a broad range of KM-related functions, including brand management, marketing strategy input and enhancing the organization's online presence.
- Data manager. Typically, this role transcends KM but also includes it. A data manager has broad authority over all of an organization's data assets and resources and oversees their structuring, maintenance and access. This includes all KM systems, where utility and accuracy are of prime importance, making the data manager an important support role for organizational decision-making.
The title knowledge manager covers a great deal of ground. There are many knowledge management career options, and many knowledge management jobs that are part of other careers, making this skill set versatile and valuable.
Learn how collaboration and knowledge management compare and how integrating these two strategies can improve employee efficiency and collaboration.