cloud networking
What is cloud networking?
Cloud networking is a kind of information technology (IT) infrastructure in which some or all of an organization's networking resources are hosted in the cloud, whether in public cloud, private cloud or a hybrid cloud combination.
Hosting networking resources in the cloud -- which can include virtual routers, network management software bandwidth, firewalls and other tools as needed -- means businesses can create complex networks using only an internet connection.
Cloud networking focuses on the ability of a cloud customer or cloud service provider to design, configure and manage the underlying network in a cloud service. This enables a shift of network management, control and data connectivity from an organization's premises to cloud infrastructure.
Networking resources or services that can be hosted in the cloud include the following:
- network management software
- connectivity
- virtual routers
- firewalls
- load balancers
- bandwidth
- content delivery networks (CDNs)
- virtual private network (VPN)
- domain name system (DNS)
Cloud providers offer a broad range of network security options . In addition to firewalls other options include distributed denial of service (DDoS) protection services and AI-driven network monitoring tools for threat detection.
Types of cloud networking
The two main types of cloud networking are cloud-enabled networking and cloud-based networking.
- Cloud-enabled networking is a cloud networking method where network architecture is on the customer's premises, but some or the rest of other network resources used for management are in the cloud. For example, core network infrastructure, such as packet forwarding and routing, would stay on premises, while services such as network management, monitoring and security services maintenance may be located in the cloud.
- Cloud-based networking is another method in which the entire network is based in the cloud. This process is used to enable connectivity between the resources and applications deployed in the cloud.
How does cloud networking work?
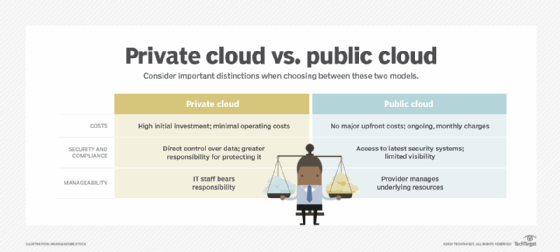
In general, cloud networking architectures should provide centralized management, control and visibility. Cloud networking is created using cloud-based services and will be set up differently depending on the type of cloud service it is being hosted on. For example, with a private cloud, architects have more flexibility when it comes to the overall design. This is because the cloud provider fully manages the underlying hardware and software on which the cloud is built.
For public clouds, customers can control and manage networking only in infrastructure as a service (IaaS) deployments. With software as a service (SaaS) and platform as a service (PaaS), the customer has no control over network functions, as they're fully managed by the service provider. If organizations need to configure aspects of their network in a public cloud, IaaS is their best option.
An organization may instead opt to operate in a hybrid cloud architecture. That means some applications, data and services reside on premises, while others are moved to an IaaS provider. The ideal scenario for organizations with this method would be to mimic the network Internet Protocol (IP) space, policies and procedures already established in their own data centers.
Some businesses may even go an additional step further by using multiple cloud service providers in a multi-cloud architecture. Symmetry among clouds is key in this method, from both an operational and cloud management perspective. Organizations moving toward multi-cloud must be able to manage routing, access lists, load balancing and other network functions, no matter which cloud they're in. Multi-cloud management tools need to be purpose-built in order to create a software overlay between private and public clouds, which masks any underlying differences in configuration management. The multi-cloud option is far more complex than other options.
Benefits and challenges of cloud networking
The benefits of cloud networking include the following:
- Lower cost. This is compared to having organizations buy their own network equipment and software. Cloud networking is also based on pay-per-use models.
- Productivity. IT staff won't have to worry about pushing hardware and software upgrades or configuration and maintenance updates to the cloud networking service. This should free an organization's IT staff to work on other network priorities.
- Reliability. Server load balancing helps minimize downtime, and reduces the need to bring the system down for updates. Cloud services also normally promote high availability (HA).
- Fast deployments. Users can access new applications without needing to spend time installing and configuring networking tools.
- Scalability. Cloud networking providers can add more of an organization's data, as opposed to adding more infrastructure on premises.
- Flexibility. Customers have the option to choose from public, private or hybrid cloud deployment.
- Security. Cloud networking providers can provide security options, such as firewalls, encryption, authentication and malware protection.
Cloud networking is not free from challenges, however. Some of the challenges can include the following:
- Vendor lock-in. Being locked into one cloud provider could prevent any needed movements or pivots among different cloud services. This can be mitigated using a multi-cloud method; however, this is more difficult to accomplish.
- Connectivity and uptime. Even though cloud providers tend to promote highly accessible services, if something goes wrong, it is out of the customer's control.
- Security. Because security is a concern with any tool, organizations should first make sure an acceptable amount of network security services are offered by the vendor they choose.
Cloud networking vs. cloud computing
Cloud networking and cloud computing are two similar concepts that can be easily confused. Cloud computing is a general term that involves delivering hosted services over the internet. These services are divided into three categories: IaaS, PaaS and SaaS. Cloud computing involves hosting in a cloud service provider's data centers rather than in traditional in-house or colocated data centers. Cloud networking is more specific, however, as it focuses on hosting an organization's networking resources in the cloud.
Cloud networking and cloud computing have a natural overlap. As an example, some functions contained in network appliances inn a legacy data center can be embedded in a cloud computing environment, as with load balancers, or delivered as a SaaS-style cloud service, as with secure web gateways or firewalls.
History of cloud networking
The history of cloud networking follows the history of cloud computing closely. Over time, corporate data center resources evolved and moved from on-premises mainframes to the cloud. The added benefits of hosting data centers in the cloud includes security, uptime, scalability and the freedom of not having to worry about on-premises deployments. Because of these benefits, more organizations began moving to the cloud. For example, software-defined networks could now be hosted in the cloud. With this movement, the option of hosting just networking systems in the cloud arose. Product offerings released by vendors such as IBM and Juniper offered software to help build agile network infrastructures. Juniper Contrail Enterprise Multicloud, for example, delivers software-defined networking cloud options, as well as cloud service automation.







