Top 11 cloud security challenges and how to combat them
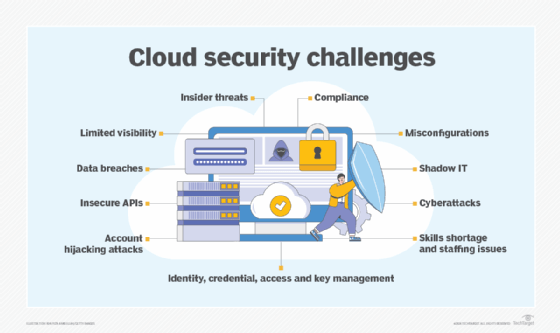
Before jumping feet-first into the cloud, understand the new and continuing top cloud security challenges your organization is likely to face -- and how to mitigate them.
All the major promises of the cloud -- improved IT efficiency, flexibility and scalability -- come with one major challenge: security.
Many organizations can't delineate where cloud service provider (CSP) responsibilities end and their own responsibilities begin, opening them to numerous vulnerabilities. The increased expansiveness of the cloud also increases an organization's potential attack surface. To further complicate the matter, traditional security controls often don't fulfill cloud security needs.
To help companies understand the cloud challenges they're up against, the Cloud Security Alliance (CSA) went directly to the professionals. A working group of practitioners, architects, developers and C-level staff identified a list of about 25 security threats, which were then analyzed by security professionals who ranked them and narrowed them down further to the 11 most common cloud security challenges:
- data breaches
- misconfigurations and inadequate change control
- lack of cloud security architecture and strategy
- insufficient identity, credential, access and key management
- account hijacking
- insider threats
- insecure interfaces and APIs
- weak control plane
- metastructure and applistructure failures
- limited cloud usage visibility
- abuse and nefarious use of cloud services
From there, CSA published its biennial report, "Top Threats to Cloud Computing: The Egregious 11," detailing the threats and whose responsibility they were -- either customer, CSP or both -- and offering steps to help organizations stay protected.
Now in its fifth iteration, the latest CSA report revealed some drastic changes. Notably, six of the 11 top threats were new to the list. In addition, none of the threats was the sole responsibility of the CSP; rather each is a responsibility of the customer or of both the CSP and customer together.
This article is part of
What is cloud security management? Guide and best practices
"We noticed the most popular trends are now things [organizations] have a little bit more control over as a customer," said John Yeoh, global vice president of research at CSA. He attributed the changes to two things: Either companies have a lot more trust in CSPs to do their jobs, or organizations like having control and want to have a better understanding of what they can do in the cloud and how they can use the cloud to meet their specific security requirements.
A far as what made this year's list, here are the top 11 threats -- listed in order of severity, according to survey respondents -- along with mitigations for each.
1. Data breaches
A responsibility of both CSPs and their customers, data breaches remained the top cloud security threat yet again this year in CSA's report. A number of data breaches have been attributed to the cloud over the past years, one of the most notable being Capital One's cloud misconfigurations.
A data breach can bring a company to its knees, causing irreversible damage to its reputation, financial woes due to regulatory implications, legal liabilities, incident response costs and decreased market value.
CSA recommended the following:
- defining data value and the impact of its loss;
- protecting data via encryption; and
- having a strong, well-tested incident response plan.
CSA Cloud Controls Matrix (CCM) specifications (see "CSA Cloud Controls Matrix" sidebar for more info) include the following:
- performing data input and output integrity routines;
- applying the principle of least privilege to access control; and
- establishing policies and procedures for secure data removal and disposal.
CSA Cloud Controls Matrix
CCM is a supporting file of CSA Security Guidance, a fourth-generation document outlining various cloud domains and their key goals and objectives.
CCM offers detailed lists of requirements and controls, categorized by control area and control ID, each mapped to its control specifications; architecture relevance; cloud delivery model(s), i.e, SaaS, PaaS and IaaS; and standards and frameworks, such as PCI DSS, NIST and FedRAMP.
Note, each Egregious 11 cloud security challenge has multiple CCM specifications. This article included only a sampling for each.
Read CSA Security Guidance, and download a copy of CCM and accompanying Consensus Assessment Initiative Questionnaire (CAIQ) for more information.
2. Misconfigurations and inadequate change control
When assets are set up incorrectly, they are vulnerable to attack. For example, the Capital One breach was traced back to a web application firewall misconfiguration that exposed Amazon S3 buckets. In addition to insecure storage, excessive permissions and the use of default credentials are two other major sources of vulnerabilities.
Related to this, ineffective change control can cause cloud misconfigurations. In on-demand, real-time cloud environments, change control should be automated to support rapid change.
A responsibility of the customer, misconfigurations and change control are new to the cloud security threat list.
CSA recommended the following:
- paying special attention to data accessible via the internet;
- defining the business value of data and the impact of its loss; and
- creating and maintaining a strong incident response plan.
CCM specifications include the following:
- ensuring external partners adhere to the change management, release and testing procedures used by internal developers;
- conducting risk assessments at planned intervals; and
- performing security awareness training with contractors, third-party users and employees.
3. Lack of cloud security architecture and strategy
Too many organizations jump into the cloud without the proper architecture and strategy in place. Prior to making the leap to the cloud, customers must understand the threats they are exposed to, how to migrate to the cloud securely -- note, it's not a lift-and-shift process -- and the ins and outs of the shared responsibility model.
This threat is new to the list and is a responsibility of the customer. Without proper planning, customers will be vulnerable to cyber attacks that can result in financial losses, reputational damage, and legal and compliance issues.
CSA recommended the following:
- ensuring the security architecture aligns with business goals and objectives;
- developing and implementing a security architecture framework; and
- implementing continuous security monitoring procedures.
CCM specifications include the following:
- ensuring risk assessment policies include updating policies, procedures, standards and controls to remain relevant;
- designing, developing and deploying business-critical/customer-impacting application and API designs and configurations and network and system components in accordance with agreed-upon service-level and capacity-level expectations, IT governance, and service management policies and procedures; and
- restricting and monitoring traffic between trusted and untrusted connections in network environments and virtual instances.
4. Insufficient identity, credential, access and key management
A majority of cloud security threats -- and cybersecurity threats in general -- can be linked to identity and access management (IAM) issues. According to CSA guidance, this stems from the following:
- improper credential protection
- lack of automated cryptographic key, password and certificate rotation
- IAM scalability challenges
- absence of multifactor authentication
- weak passwords
New to the top cloud security challenges list, standard IAM challenges are exacerbated by cloud use. Conducting inventory, tracking, monitoring and managing the sheer number of cloud accounts needed is compounded by provisioning and deprovisioning issues, zombie accounts, excessive admin accounts and users bypassing IAM controls, as well as challenges with defining roles and privileges.
As a customer responsibility, CSA recommended the following:
- using two-factor authentication;
- practicing strict IAM controls for cloud users and identities;
- rotating keys, removing unused credentials and access privileges, and employing central, programmatic key management.
CCM specifications include the following:
- identifying key managers and creating and maintaining key management policies;
- assigning, documenting and communicating the roles and responsibilities for performing employment termination or procedure changes; and
- performing timely deprovisioning -- whether revocation or modification -- of user access to data and network components.
5. Account hijacking
Cloud account hijacking is the disclosure, accidental leakage, exposure or other compromise of a cloud account that is critical to the operation, administration or maintenance of a cloud environment. These highly privileged and sensitive accounts, if breached, can cause massive consequences.
From phishing and credential stuffing to weak or stolen credentials to improper coding, account compromise can lead to data breaches and service disruptions.
A responsibility of CSPs and customers, CSA recommended the following:
- remembering that account hijacking isn't just a password reset; and
- using defense-in-depth and IAM controls.
CCM specifications include the following:
- establishing, documenting and adopting a unified business continuity plan;
- separating production and nonproduction environments; and
- maintaining and regularly updating compliance liaisons in preparation for a forensic investigation requiring rapid engagement with law enforcement.
6. Insider threats
The risks associated with employees and others working within an organization's network are not limited to the cloud. Whether negligent or intentional, insiders -- including current and former employees, contractors and partners -- can cause data loss, system downtime, reduced customer confidence and data breaches.
A responsibility of the customer, insider threats involving leaked or stolen data, credential issues, human errors and cloud misconfigurations must be addressed.
CSA recommended the following:
- conducting security awareness training;
- fixing misconfigured cloud servers; and
- restricting access to critical systems.
CCM specifications include the following:
- requiring authorization prior to relocating or transferring hardware, software or data;
- authorizing and revalidating user access controls at planned intervals; and
- segmenting multi-tenant apps, infrastructure and networks from other tenants.
CSA Egregious Eleven
Download the full Egregious 11 report from CSA.
This deep dive examines nine real-world attacks and breaches that exemplify the Egregious 11 threats.
7. Insecure interfaces and APIs
CSP UIs and APIs through which customers interact with cloud services are some of the most exposed components of a cloud environment. The security of any cloud service starts with how well these are safeguarded and is the responsibility of both customers and CSPs.
CSPs must ensure security is integrated, and customers must be diligent in managing, monitoring and securely using what CSA calls the "front door" of the cloud. This threat dropped from the third most important in the last report but is still important to address.
CSA recommended the following:
- practicing good API hygiene;
- avoiding API key reuse; and
- using standard and open API frameworks.
CCM specifications include the following:
- designing, developing, deploying and testing APIs in accordance with industry leading standards, as well as adhering to applicable legal, statutory and regulatory obligations;
- segregating and restricting access to audit tools that interact with the organization's information systems to prevent data disclosure and tampering; and
- restricting utility programs capable of overriding system, object, network, VM and application controls.
8. Weak control plane
A responsibility of the customer and new to the list this year, the cloud control plane is the collection of cloud administrative consoles and interfaces used by an organization. It also includes data duplication, migration and storage, according to CSA. Improperly secured, a breached control plane could cause data loss, regulatory fines and other consequences, as well as a tarnished brand reputation that could lead to revenue loss.
CSA recommended the following:
- requiring adequate controls from CSPs; and
- performing due diligence to determine if potential cloud services have adequate control planes.
CCM specifications include the following:
- establishing and making infosec policies and procedures readily available for review by internal personnel and external business relationships;
- implementing and applying defense-in-depth measures to detect and respond to network-based attacks in a timely manner; and
- establishing policies to label, handle and secure data and objects that contain data.
9. Metastructure and applistructure failures
The metastructure, defined by CSA, is "the protocols and mechanisms that provide the interface between the infrastructure layer and other layers" -- in other words, "the glue that ties the technologies and enables management and configuration."
Also known as the waterline, the metastructure is the line of demarcation between CSPs and customers. Many security threats exist here -- for example, CSA cited poor API implementation by CSPs or improper cloud app use by customers. Such security challenges could lead to service disruption and misconfigurations with financial and data loss consequences.
The applistructure is defined as "the applications deployed in the cloud and the underlying application services used to build them -- for example, PaaS features like message queues, AI analysis or notification services."
A new threat this report, it is a customer and CSP responsibility. CSA recommended the following:
- CSPs offering visibility and exposing mitigations to counteract their tenants' lack of transparency;
- CSPs conducting penetration testing and providing findings to customers; and
- customers implementing features and controls in cloud-native designs.
CCM specifications include the following:
- developing and maintaining audit plans to address business process disruptions;
- implementing encryption to protect data in storage, in use and in transit; and
- establishing policies and procedures to store and manage identity information.
10. Limited cloud usage visibility
Cloud visibility has long been a concern of enterprise admins, but it is new to the CSA cloud security challenges list this report. Limited visibility results in two key challenges, according to CSA:
- Unsanctioned app use, also known as shadow IT, is when employees use applications not permitted by IT.
- Sanctioned app misuse is when apps approved by IT are not used as intended. This includes users authorized to use the app, as well as unauthorized individuals accessing it with stolen credentials obtained via SQL injection or DNS attacks, for example.
This limited visibility, CSA said, leads to lack of governance, awareness and security -- all of which can result in cyber attacks, data loss and breaches.
New to the list this year, it is a responsibility of CSPs and customers. CSA recommended the following:
- developing a cloud visibility effort from the top down;
- mandating and enforcing companywide training on acceptable cloud usage policies; and
- requiring all nonapproved cloud services be reviewed and approved by a cloud security architect or third-party risk management.
CCM specifications include the following:
- conducting risk assessments at regular intervals;
- making all personnel aware of their compliance and security roles and responsibilities; and
- conducting inventories, documenting and maintaining data flows.
11. Abuse and nefarious use of cloud services
Just as the cloud can be used for good, it can also be used maliciously by threat actors. Nefarious use of legitimate SaaS, PaaS and IaaS offerings affects individuals, cloud customers and CSPs alike. Disguised as coming from a CSP, customers are especially vulnerable to the misuse of cloud services via the following:
- distributed denial-of-service attacks
- phishing
- cryptomining
- click fraud
- brute-force attacks
- hosted malicious or pirated content
Compromised and abused cloud services can lead to incurred expenses -- for example, loss in cryptocurrency or payments made by the attacker; the customer unknowingly hosting malware; data loss; and more.
CSA recommended CSPs be diligent in detecting and mitigating such attacks with an incident response framework. CSPs should also offer tools and controls their customers can use to monitor cloud workloads and applications.
A customer and CSP responsibility, CSA recommended the following:
- monitoring employee cloud use; and
- using cloud data loss prevention technologies.
CCM specifications include the following:
- adopting technical measures to manage mobile device risks;
- defining allowances and usage permissions for enterprise- and user-owned endpoints, including workstations, laptops and mobile devices; and
- creating and maintaining a list of approved applications and application stores.







