The cloud shared responsibility model for IaaS, PaaS and SaaS
The shared responsibility model defines cloud security, but it changes for IaaS, PaaS and SaaS. Get to know the ins and outs of cloud security and learn exactly what your company is responsible for.
With so many vendors, platforms, tools and services that fall under IaaS, PaaS and SaaS categories, enterprises need to understand the sliding scale of security responsibilities in the cloud.
With traditional on-premises data centers, a company's IT staff is completely in charge of all data as well as the physical infrastructure. These clearly defined barriers make the whole security process relatively straightforward. When they move to the cloud, IT teams have to deal with infrastructure and services from cloud providers, which tends to complicate an organization's overall security strategy.
Once a cloud provider gets involved, the vendor also takes on some of the responsibility related to securing your environment -- but not necessarily the data held within it. This can be extremely helpful for many IT teams, but if administrators and developers don't secure their end of things, their companies can become vulnerable to breaches.
The key to a successful cloud security strategy is understanding the cloud shared responsibility model to the fullest extent.
IaaS, PaaS and SaaS security models
Before diving into the details of a cloud shared responsibility model, IT teams must understand the security differences within the different types of cloud service models -- IaaS, PaaS and SaaS. These services dictate what a company is -- or is not -- responsible for. A quick key to remember is that generally, users' responsibility increases as they move down the stack, from SaaS to IaaS.
This article is part of
What is cloud management? Definition, benefits and guide
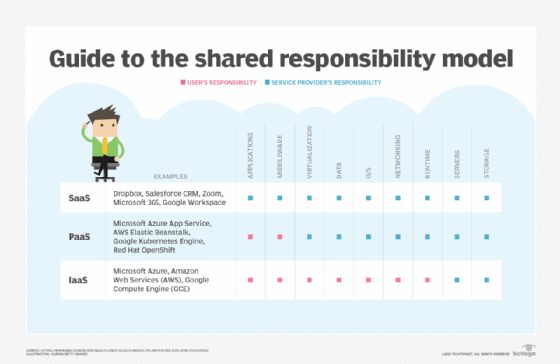
With an IaaS model, the vendor is responsible for security of the physical data centers and other hardware that power the infrastructure -- including VMs, disks and networks. Users must secure their own data, operating systems and software stacks that run their applications. In this deployment model, users maintain control over many aspects of their workloads but have the luxury of leaning on their cloud provider to manage security from both a physical and virtualization standpoint.
PaaS is the middle ground when it comes to the cloud shared responsibility model, placing more responsibility in the hands of the cloud provider. In this scenario, IT teams still deploy and manage their applications and related data, but the provider secures the operation of the underlying infrastructure and overall operating systems.
In the SaaS model, administrators have less control over the software stack. The SaaS vendor is responsible for securing the application and the supporting infrastructure. IT teams only have to worry about managing their data and security permissions.
Enforcing the model
Cloud security threats and cyberattacks are on the rise, according to a 2020 McAfee study. Most high-profile security breaches, which tend to be very costly for the affected enterprise, are caused by a misstep on the part of the user -- not the cloud provider.
Working with a cloud provider can be uncharted territory for some organizations. From the start, they need to outline for their staff exactly where their cloud provider's security ends and where their domain begins. This is also where organizations must make sure their staff is thoroughly trained on their chosen cloud -- as well as any related tools and services -- to avoid any preventable issues down the line.
When it comes to a cloud shared responsibility model, there is no room for assumption and users should not leave anything up in the air. To ensure they are on the same page with their chosen cloud vendor, IT teams should reference their service-level agreements. Clear up any confusion with the provider when necessary to ensure a security strategy is successful from both sides of the vendor-customer relationship.








