What is cloud security management? Guide and best practices
This cloud security guide explains challenges enterprises face today, best practices for securing and managing SaaS, IaaS and PaaS, and comparisons of cloud-native security tools.
Organizations of all sizes have adopted cloud strategies to varying degrees. While beneficial in many ways, the cloud also has its risks, which organizations should fully assess before placing assets there. In this comprehensive guide, complete with links to more information, we lay out the challenges in securing the cloud environment as well as how to develop best practices for managing cloud security.
What is cloud security management?
Cloud security management is not a single concept or product. It is actually a complementary combination of strategies, tools and practices that are intended to help a business host workloads and data in a cloud efficiently and cost-effectively -- yet limit the threats and vulnerabilities that are often present in complex public networks as well as shared cloud resources and services. Cloud security is a multifaceted endeavor that involves numerous efforts, including the following:
- Authentication and authorization. This is comprehensive user management based on cloud services, such as identity and access management (IAM), to ensure that any cloud users or devices are authorized to access workloads and data.
- Data security. Use encryption to guard valuable business data against theft, loss, or other unauthorized access.
- Suitable cloud architectures. Compose cloud architectures and connect security services that are appropriate and properly configured for each workload being hosted.
- Proper application configuration. Beyond the proper configuration of cloud resources and services, each workload hosted in the cloud will also possess varied configuration options that must be set and maintained properly.
- Monitoring and reporting. Cloud security requires comprehensive tooling to guard against malicious activity, maintain data integrity, and produce real-time alerts and ongoing reporting in response to detected security issues.
Why is security management in the cloud important?
Far too often, organizations place their trust in cloud providers to ensure a secure environment. Unfortunately, that approach has numerous problems -- namely, that cloud providers don't always know the risk associated with a customer's systems and data. They don't have visibility into other components in the customer's ecosystem and the security requirements of those components. Failing to take ownership of cloud security is a serious downfall that could lead organizations to suffer data loss, system breaches and devastating attacks.
The irony here is that many organizations approach cloud computing thinking that the business can offload the problems and responsibilities of everyday computing. While this is true to an extent with issues such as facilities maintenance and capital expenditure mitigation, it's not true with issues such as data compliance and security. A business bears responsibility for the security and compliant use of its data in the cloud -- just as a taxpayer bears responsibility for the accuracy and completeness of their tax returns, even when those documents are prepared by someone else.
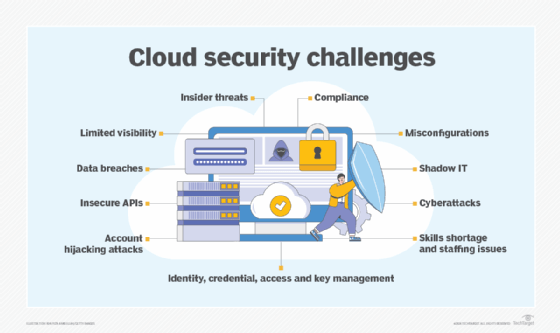
The Cloud Security Alliance (CSA) shared the most common cloud security challenges to give organizations a sense of the massive attack surface cloud computing presents. In addition to the potential for data breaches and lack of visibility, the following are some of the most egregious problems the alliance found:
- Misconfigurations and inadequate change controls.
- Lack of cloud security architecture and strategy.
- Insufficient identity, credential, access and key management.
- Account hijacking.
- Insecure interfaces and APIs.
- Abuse and nefarious use of cloud services.
The fallout from cloud attacks is often exponential, and the blast radius of attacks continues to expand. For example, "an attack on a single user's credentials reaches far beyond the targeted victim, often affecting the entire organization and its customers," wrote Dave Shackleford, principal consultant at Voodoo Security. Recent attacks also illustrate an immaturity of organizations' ability to defend their cloud environments, he added.
The type of cloud environment an organization selects must be well considered because private, public and hybrid options each have pros and cons. For instance, a public cloud strategy can lighten the load on an organization's IT team since they don't have to manage systems in-house. A public cloud provider might not be as particular as the organization about security, however, which could leave gaps in the organization's protection.
With a private cloud environment, an organization might gain more control over security, but cloud costs and complexity will likely rise as a result. And while a hybrid approach -- part public, part private -- might seem like the perfect compromise, it presents challenges, too, including policy enforcement across environments.
What are the benefits of cloud security management?
Cloud security can be complex and demanding, but there are important benefits that any enterprise should consider:
- Better visibility. Comprehensive and well-designed cloud security management can provide cloud users with detailed and documented insight into their cloud deployments. For example, users can obtain a reliable picture of the workloads and data present in the cloud, what resources and services are involved, how those resources and services are configured, who is accessing the workloads and data, and what data is being accessed.
- Better compliance. Visibility information can be priceless for ensuring regulatory compliance and performing forensic analysis of incidents. Business users can understand the factors involved in an incident, correct deficiencies and take decisive action to remediate the impact of an incident for customers and regulators.
- Better tools. Many cloud providers offer comprehensive security tools -- built specifically to operate within the providers' infrastructure -- which can scan, analyze, report and alert on potential security threats with a high degree of effectiveness. This alleviates the need for users to install and operate their own security applications or tools in the cloud.
- Security services. Cloud providers typically offer data encryption and other services, such as data loss prevention (DLP) designed to protect business data at rest and in flight. Other services such as data backups, recovery and disaster recovery (DR) can further help to protect vital business data in the cloud.
- Lower security costs. Businesses can often lower security costs and improve security effectiveness when using the security tools and services supplied through cloud providers, which are typically updated more frequently and tested more comprehensively than security tools deployed in local data centers or deployed to the cloud as user-based workloads.
What are the challenges of cloud security management?
Cloud security faces an ever-growing array of challenges. Businesses that use the cloud (or are considering cloud deployment targets) should take the time to seriously consider many of the most important security challenges, including the following:
- Shared responsibility. Clouds operate on a shared responsibility model, but there are often misunderstandings about responsibilities and definitions that lead to critical gaps in security management. It's important to understand the shared responsibility model clearly and work with providers to ensure that each side meets its obligations.
- Limited visibility. If you can't see it, you can't manage it: It's an old axiom that perfectly suits cloud security efforts. A business must be able to see where all of their applications and data are located in the cloud, and this can be problematic with such decentralized control over different business teams and divisions that might use the cloud. There must be a means of discovering, tracking, and reporting on the assets present in the cloud.
- Compliance challenges. A business is obligated to know what assets it has available, where those assets are located, and how they're being used. When a cloud provider obscures this information (or a user does not bother to access this information), the business could experience a costly breach in regulatory compliance. It's important to understand the tools and visibility offered by a provider and to understand how that information can meet compliance requirements.
- Limited control. Businesses do not own the cloud infrastructure. While a user can assert considerable control over some security issues like user authorization and authentication, users typically do not assert control over the underlying cloud infrastructure as they would within a local data center. This can lead to security concerns in how data is accessed and shared.
- Cloud differences. Every cloud is different. As businesses explore hybrid and multi-cloud environments, there are bound to be differences in tools, services, configurations and capabilities that might cause an inconsistent or incomplete security posture for the business. This is another case where consultations with the providers can be extremely beneficial for business users.
Best practices for cloud security
Once an organization has committed to a cloud environment for data, applications, platforms and infrastructure, the next task is to create a cloud security policy. The policy should address critical considerations, such as how employees can interact with the cloud, the types of data that can be sent and stored there, access controls and more.
While developing a cloud security policy can be done using many approaches, including adapting an existing infosec policy or using a software package, independent IT consultant and auditor Paul Kirvan created a cloud security policy template that walks organizations through policy creation.
How you address cloud security is also dependent on the type of cloud service an organization needs: SaaS, IaaS or PaaS.
SaaS security best practices. SaaS is not a monolithic service and shouldn't be treated as such when it comes to security. There are many types of SaaS, and the performance of SaaS providers can vary dramatically. Instead, organizations need to look at a roster of guidelines and apply the ones that best fit the service being adopted. Ed Moyle, systems and software security director at Drake Software, laid out the following best practices to protect SaaS-based applications:
- Vet and oversee potential providers.
- Deploy enhanced authentication, such as multifactor authentication (MFA), where possible.
- Encrypt data in motion and at rest in the cloud.
- Utilize manual and automatic methods to discover and inventory cloud assets.
SaaS also requires a corporate culture where IT and security teams work together to secure a cloud-based business application.
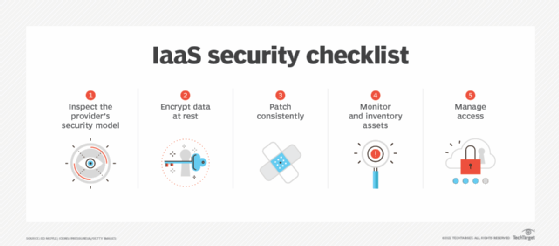
IaaS security best practices. Like SaaS, IaaS requires organizations to consider how to encrypt data at rest and inventory cloud assets, but securing infrastructure in the cloud requires even more attention to security. IaaS gives users extensive access to the provider's resources and services, which can be composed as desired to create an operating environment suitable for hosting a business workload and data. Organizations need to develop an IaaS security checklist to ensure consistent patching and access management. IaaS has many access layers to be managed, including access to the IaaS console and specific features such as backup and recovery.
PaaS security best practices. PaaS security guidelines recommend that organizations be deeply involved in the protection of their platform services and not leave the details up to the provider. For example, enterprises should engage in threat modeling and the deconstruction of an application design, which will help identify vulnerabilities and mitigate them. The PaaS provider will offer security tooling and capabilities, but it's up to the PaaS users to actually employ those features.
Another key best practice for PaaS users is to carefully plan out portability so the organization isn't bound to one provider. For example, software development PaaS users might choose to work with common programming languages -- such as C#, Python and Java -- that are supported across software development PaaS providers.
Who is responsible for cloud security?
Today, the cloud computing industry operates on a "shared responsibility" model. The model generally dictates that a cloud provider is responsible for security of their cloud, while cloud users are responsible for security in the cloud. It might seem like a fine distinction, but it's a vital one to understand:
- A cloud provider is responsible for ensuring that its infrastructure and services are operating in a secure manner. For example, the provider's servers and networks must be set up and configured securely.
- A cloud user is responsible for ensuring that they use the security features and capabilities needed to operate their workloads and access their data in a secure manner.
As an example, suppose a cloud provider offers IAM services to help customers manage user access to workloads and data. The user must employ those IAM services. If the customer chooses to forego those IAM services -- and effectively opens access to workloads and data to anyone -- the business cannot reasonably expect to maintain cloud security. This might even violate compliance and other regulatory obligations for the customer's business, but the cloud provider is not responsible for any data loss or theft.
Enterprise IT staff are often tasked with cloud security issues. While traditional enterprise security teams can take on some cloud security duties, protecting cloud data and operational workloads requires a specific skill set.
Organizations should create a cloud IAM team dedicated to certain aspects of cloud security, such as access, authentication and authorization. Shackleford recommended that the cloud IAM team, which could tackle single sign-on (SSO) and federation, should be started with existing internal groups because they have a deep understanding of the business and its goals.
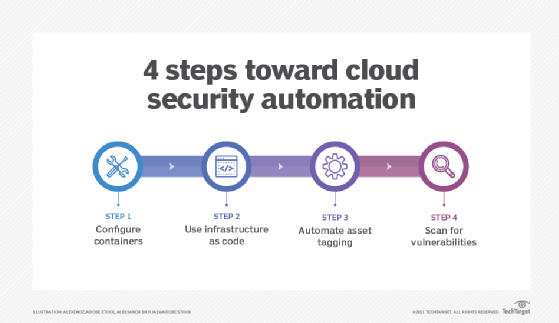
A dedicated IaaS team might also address cloud security automation in four key areas:
- Container, virtual machine and serverless computing configuration.
- Infrastructure as code (IaC) and other automated infrastructure composition techniques.
- Asset tagging and other cloud inventory management tactics.
- Vulnerability scanning.
Setting and managing IaaS controls and processes in these areas enables smooth and consistent deployments, proper auditing and reporting, and policy application and enforcement.
These special-purpose teams should follow cloud compliance standards closely, making sure cloud service providers are up on the latest industry requirements. Read about the top cloud security standards bodies and their areas of compliance oversight.
Cloud security training has improved in recent years, and targeted certifications can demonstrate a professional's cloud security chops. For instance, ISC2 has a Certified Cloud Security Professional (CCSP) certification, and the CSA offers a Certificate of Cloud Security Knowledge. CompTIA, Arcitura and Exin also have programs, as do vendors such as Amazon, Google and Microsoft.
Cloud security-savvy professionals can test their bona fides with these CCSP exam questions.

Cloud security management strategies
Rarely do organizations have a single cloud environment; it's more likely that they have multiple ones that address various data, application, platform and infrastructure needs. Managing disparate cloud services can be challenging, so organizations need a sound strategy that protects corporate assets while maintaining compliance and managing costs.
To prevent or rein in sprawl, organizations should centralize the procurement, deployment and management of their multi-cloud environments. Doing so can ensure an organization's security policies and compliance requirements are applied and enforced. Centralizing also is critical for organizations to be able to collaborate and communicate in a uniform way about threats and mitigation strategies. Emerging FinOps practices can help establish collaborative cross-discipline teams tasked with managing cloud use and cost management.
Cloud security teams need to test their cloud environments regularly. Nemertes Research founder and president Johna Till Johnson encouraged companies to tap into specialized tools that enable organizations to run hostile tests against their environments. These tools help shore up the cloud environment. She also suggested performing live-fire training -- where cloud environments are made deliberately insecure -- so security professionals can learn how to combat threats and discover weaknesses and gaps in the environment as well as their skills in real time.
Testing also is essential for the shared responsibility model, where in-house and provider security teams together assume the role of protecting assets in the cloud. Cloud penetration testing is a useful way to test the shared responsibility model and the security of a cloud environment overall.
Some organizations in highly regulated or high-risk industries might want to employ forensics techniques in their cloud environment to support investigations. Automation should be top of mind for this goal so that organizations can not only inspect and analyze information in the cloud for court proceedings (e.g., network packets, workload memory, workload disk volumes, logs and other event data) but also mitigate any issues based on what is discovered.
One of the most significant types of attacks security teams must ward off through better cloud security management is cloud account hijacking, in which hackers compromise a subscription or other type of cloud account to engage in malicious activities. The following three key strategies can protect an organization from such an incident:
- Use multifactor authentication.
- Segregate duties.
- Trust but verify account access.
One often overlooked aspect of cloud security testing and security management is information sharing. Although there are many tools and practices that can help to find and fix security issues, answers to the following questions can easily be lost or ignored unless it is documented and shared across the cloud management team:
- What happened?
- Why did it happen?
- What was the root cause?
- What was the remediation?
- What were the results?
- How should policy, practice and process change moving forward?
Information sharing enables the entire cloud management team to benefit and learn from issues or incidents that affect cloud security.
Implementing cloud security management
There is no single means of implementing and managing cloud security. The approaches are as varied as the tools and the business that use them. However, there are several guiding principles that can be applied to implementation:
- Understand the business drivers and goals. This is another way of "starting with the end in mind." Cloud security -- and its proper management -- are there for a purpose, which is to serve the business and facilitate business interests. Any implementation of cloud security management should be in response to business needs. For example, compliance might be a primary security goal for a highly regulated business.
- Understand the threats. It's hard to guard something if you don't know what the risks and threats are. From malware to intrusion to disasters, it's vital to understand where the attacks will come from and how those attacks put the business -- and its goals -- at risk. Perform regular security audits on cloud-based workloads, data and services. Identifying the threats will make new policies and processes easier to build and help narrow the selection of the most suitable tools for the job.
- Create security principles and practices. Consider how the business should approach cloud security, such as accessing and protecting data. Chances are that cloud security and security management will vary from traditional data center security, so think ahead and evaluate how cloud security processes should best work for the business.
- Select and implement tools. There are plenty of tools, platforms and services available to help implement and manage cloud security. One size does not fit all, and each product offering has unique strengths and tradeoffs. However, knowing the business goals and intended practices makes the job of finding and validating cloud security management tools considerably easier. This could still require some adjustments to principles and practices, but the underlying ideas should be consistent.
- Encrypt data and monitor. Data should ideally be encrypted at rest and in flight. User and workload access should adopt zero-trust and other highly restricted postures. Monitor network traffic and watch for intrusion. Scan for malicious activity, such as unauthorized data access. Oversee end users and devices.
- Report. Use the alerting and reporting features of the cloud security management system to deliver timely security reports to cloud workload stakeholders and business leaders. Recognize the threats (e.g., an unpatched operating system) and take proactive action to mitigate those risks on an ongoing basis.
- Reevaluate. Threats and business needs are always changing, and so should cloud security. As cloud security evolves, the cloud security management effort should also change in order to address new and emerging threats. This is often a team effort that involves business, technology and legal leadership from across the business.
Cloud security tools
Many enterprise tools try to extend security to the cloud, but cloud-native tools can provide more seamless and comprehensive protection for cloud assets.
Cloud access security brokers
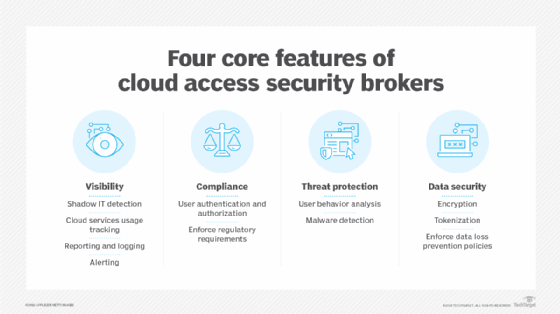
Cloud access security brokers (CASBs) serve as a security policy enforcement gateway to ensure users' actions are authorized and compliant with company policies. They have four main characteristics: visibility, compliance, threat protection and data security.
CASBs also have business-critical use cases, such as cloud application usage tracking and user behavior analytics. Purchasing a CASB requires careful consideration, and to help, Kevin Tolly, founder of The Tolly Group, shared some CASB buying tips and vendor comparisons.
For multi-cloud deployments read these tips for evaluating CASB tools.
Cloud security posture management tools
Cloud security posture management (CSPM) tools enable companies to perform continuous compliance monitoring, prevent configuration drift, set limits on permittable configurations or behavior in the cloud and support security operations center investigations.
Organizations can use CSPM tools to uniformly apply cloud security best practices to increasingly complex systems, such as hybrid, multi-cloud and container environments.
Zscaler, Orca Security and Trend Micro are some of the vendors offering CSPM tools.
Cloud workload protection platforms
A cloud workload protection platform (CWPP) unifies management across multiple cloud providers, packages controls together with workloads and ensures controls are designed to be cloud native.
CWPPs have the following benefits:
- Reduced complexity.
- Consistency.
- Portability.
Cloud security management vendors
There are countless vendors and products available for cloud security management. Each product, platform or service focuses on unique specialties or use cases; might offer some overlap in CASB, CSPM, or CWPP areas; and carries its own unique tradeoffs for enterprise users. As with most enterprise tools, it's worth evaluating a number of offerings and investing in proof-of-concept projects to identify and validate preferred products before making a commitment.
Examples of CASB vendors and tools include the following:
- Avast Secure Internet Gateway.
- Cato SASE Cloud.
- Citrix Secure Workspace Access.
- Citrix Workspace Essentials.
- Forcepoint One.
- Fortinet FortiCASB.
- Microsoft Defender for Cloud.
- Netskope.
- Oracle CASB Cloud Service.
- Proofpoint Cloud App Security Broker.
- SonicWall Cloud App Security.
- Symantec CloudSOC CASB.
- Symantec Cloud Secure Web Gateway.
- Trend Micro Cloud App Security.
Examples of CSPM vendors and tools include the following:
- Check Point CloudGuard.
- CrowdStrike Falcon Cloud Security.
- Cyscale.
- InsightCloudSec.
- Lacework Polygraph Data Platform.
- Microsoft Defender for Cloud.
- Orca Security.
- Palo Alto Networks Prisma Cloud.
- Sonrai Security.
- Sysdig Secure.
- Tenable Cloud Security.
- Trend Micro Cloud One Conformity.
- Zscaler Posture Control.
Examples of CWPP vendors and tools include the following:
- AWS Control Tower.
- AWS GuardDuty.
- Check Point CloudGuard Network Security (IaaS).
- CrowdStrike Falcon Cloud Security.
- Google Cloud Security Overview.
- Illumio Core.
- Microsoft Defender for Cloud.
- Orca Security.
- Palo Alto Networks Prisma Cloud.
- PingSafe.
- SentinelOne Singularity Cloud.
- Sophos Cloud Workload Protection.
- Trend Micro Deep Security.
- VMware Carbon Black Workload.
Editor's note: The lists shown here have been assembled from varied research sources and are intended to provide examples only; they are not intended to represent all available products in a given area. Readers are advised to perform their own research and make product selections based on their own needs, research and testing results.





