ra2 studio - Fotolia
5 tips to optimize your hybrid cloud management
Hybrid can be an appealing -- yet daunting -- cloud architecture for IT teams looking for flexibility. Review these five best practices to ensure you maximize the benefits without compromising your workloads.
Enterprises are attracted to hybrid cloud because it enables them to mix and match on-premises infrastructure, private cloud resources and public cloud services to build a cloud architecture that best fits their needs.
But since these architectures involve multiple components of different types, hybrid cloud management is often harder than operating within a single environment, whether it's on premises or in a public cloud.
Explore these five best practices for managing hybrid cloud infrastructure so your IT team can optimize for reliability, performance, cost and security. Whether you plan to build a hybrid cloud from scratch or have an existing hybrid cloud to manage, you'll find the tips below useful.
Carefully manage data ingress and egress
Data ingress and egress refers to the movement of data into or out of the cloud. In a hybrid cloud architecture, data ingress and egress occur whenever data moves from one component to another. For example, when an admin moves data from a public cloud service to an on-premises server or private cloud.
Data ingress and egress are important to hybrid cloud management for two main reasons:
- Performance: Data movement over the network is often the weakest link when it comes to cloud performance. Data moves much slower over an internet connection that links two disparate clouds than it does within the same cloud. This means that unnecessary data ingress and egress can undercut performance.
- Cost: In most cases, public cloud providers don't charge for incoming data transfers, but they will charge fees every time data leaves their clouds. Thus, the more data egress you experience, the higher your cost will be for the public cloud portion of your infrastructure.
To optimize for performance and cost in a hybrid cloud environment, it's critical to avoid unnecessary data transfers. If data frequently moves between parts of your hybrid infrastructure, rearrange the structure to mitigate movement between components. For example, if you have an application hosted in the public cloud that connects to a database hosted on premises, you could move the database into the public cloud to reduce data ingress/egress because the application and the database would run in the same environment.
Avoid native cloud tools
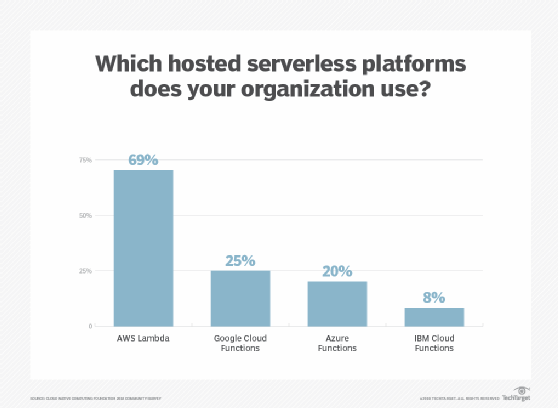
Public cloud vendors offer an array of tools to monitor and manage workloads hosted on their clouds. These services are great if your workloads run exclusively on a specific cloud, but native tools specialized for use in AWS, Google Cloud Platform or Microsoft Azure usually only help you manage the parts of your infrastructure that are in that cloud. They won't work with private clouds or on-premises resources.
Overcome these limitations by building your hybrid cloud management and monitoring toolset around third-party offerings that are compatible with a broad range of host environments. Most modern tools for application performance management, cost monitoring and provisioning work equally well with on-premises environments, private clouds and all major public clouds.
Embrace continuous change
Organizations adopt a hybrid cloud strategy to maximize flexibility, so they shouldn't treat their hybrid infrastructure as if it's set in stone.
Instead, think of hybrid cloud as an infrastructure that can and should change continuously. Don't be afraid to rebalance or reconfigure the layout of your workloads as your needs evolve and new opportunities become available.
For example, you may decide to store data on premises when you originally set up your hybrid cloud architecture. But you soon find, thanks to decreases in public cloud storage costs, that it now makes more sense to move the data to a public cloud. Or, you may have applications currently hosted on premises that could gain a performance boost by taking advantage of serverless functions based in the public cloud. Alternatively, you might decide to move data hosted on a public cloud to your private data center due to privacy and governance concerns.
Implement a cloud governance policy
The more layers you have in your cloud architecture -- as hybrid cloud can often demand -- the harder it is to ensure they're all configured in a predictable and consistent way. Configurations that lack predictability and consistency are difficult to optimize for cost, performance and security.
You can mitigate this hybrid cloud management challenge with a solid governance policy for creating or managing resources within any part of your infrastructure. It helps ensure consistency and standardization.
For example, your policy might include rules that define how to configure access rights to a new resource. That way, admins can refer to the governance policy to determine which approach to take. This helps avoid situations where you have one approach for on-premises workloads, another for private cloud workloads and another still for public cloud services.
Consider an abstraction layer
If you find that managing your hybrid infrastructure is particularly challenging, it may be worth adopting tools that unite the disparate underlying components of your infrastructure into a single interface. This makes it easier to manage the different parts of your hybrid cloud, because admins only interact with the abstraction layer instead of each underlying component.
In this sense, the use of cloud abstraction layers is similar to using virtual machine hypervisors to build a virtualized infrastructure that is consistent and uniform, even if the individual servers that host it are not.
Abstraction platforms for hybrid clouds remain relatively primitive, and setting them up requires effort. However, tools such as Libcloud can simplify application deployments across an architecture that includes multiple cloud APIs. Third-party infrastructure-as-code tools, such as Terraform, can also be adopted to standardize the deployment process for workloads across the different layers of a hybrid cloud. And, in some cases, you can use platforms like Kubernetes to unify disparate hybrid cloud components into a single environment by creating a deployment that spans your entire hybrid cloud.








