Roman Sakhno - Fotolia
Four signs you need a third-party cloud management platform
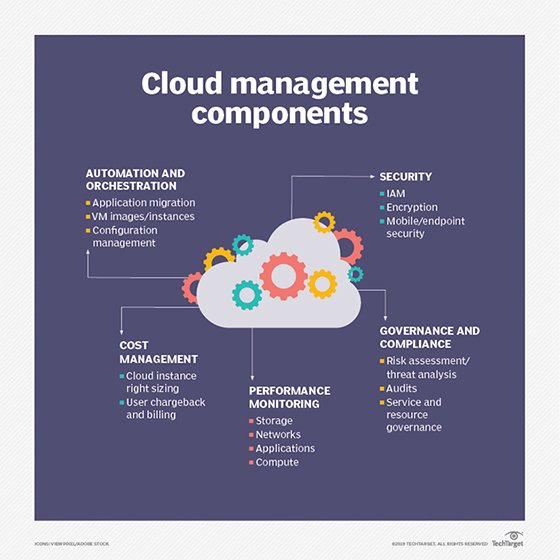
In a multi-cloud deployment, IaaS providers' native tools for admins often fall short. These four signs indicate it's time to invest in a third-party cloud management tool.
When you move to a multi-cloud model, and the number of services you use exceeds your ability to properly manage them, you've reached a tipping point. That's when it's time to evaluate a third-party cloud management tool.
Of course, that exact "tipping point" will vary from one organization to the next, depending on factors such as size, the complexity of the services under management, security and governance, as well as the skill sets of those who operate your cloud resources.
So how do you determine when it's time to implement a third-party cloud management platform? Here are four common signs to look for.
Unhappy developers
One of the most obvious signs you need a third-party tool to reduce multi-cloud complexity is developers who are frustrated by the time it takes to allocate resources to applications.
If you're an IT manager, assess how many emails you get per week from developers requesting access to cloud resources, such as storage or compute. If you get a lot, and still use native public cloud tools to deploy resources, you often have to put these requests into a queue and assign them to staff who specialize in that particular public cloud platform -- usually AWS, Azure or Google. Without proper management, these requests pile up and cause delays.
A better approach is to use a unified cloud management platform, such as Dell Cloud Manager, IBM Cloud Orchestrator or Scalr Enterprise. While these tools have their differences, each simplifies the management of hybrid and multi-cloud infrastructure through provisioning services that let admins bypass public cloud providers' native consoles. In addition, admins can use these tools to delegate access to developers and enable dev teams to allocate cloud resources directly, rather than wait for somebody else to do it for them.
Increased risk
If you have a multi- or hybrid cloud architecture and struggle to properly manage all your resources, your chances of a security breach rise. This is because accountability is often tossed out the window as teams lose track of who's responsible for which resources within a cloud deployment.
Proper IT security requires you to outline your requirements, with a full understanding of which cloud resources are in play and who is responsible for securing them. A third-party cloud management platform, including those mentioned above, can help you track which users are provisioning which resources -- as well as the steps they've taken to secure them.
Performance complaints
If you've received more than a few performance-related complaints from end users, it's time to consider a cloud management platform or additional monitoring tools. These complaints generally originate when an application doesn't receive the amount of cloud resources it needs, and thus the application saturates allocated resources.
Rookie mistakes
Automation and abstraction of multi-cloud resources frees IT pros from manual, tedious work. This means that you should be making fewer mistakes, not more, in the cloud. If you spend your day putting out fires from tactical mistakes, such as missing resource allocations required to run cloud jobs, it's likely time for a cloud management and monitoring tool.
Admins can solve this through automated resource allocation based on performance metrics. When an application approaches the limitations of a cloud instance, instances launch to fulfill the application's requirements. Most cloud management platforms have auto-provisioning and cloud orchestration capabilities that can help you achieve this.
Confusion around cost allocation
If you find yourself disputing who on your team is responsible for which part of your monthly cloud , it's likely time to invest in a third-party management tool.
In a multi-cloud environment, it's critical to have accounting visibility across IaaS providers. Enterprises need to track and log which services are in use, who uses them and how much they cost. While cloud providers offer native cost accounting features, a third-party cloud management tool with governance capabilities is key to monitor costs, enforce limitations, and handle show-backs and charge-backs by department or user.